-

Filling in the Crime Intelligence Gaps with Entity Extraction
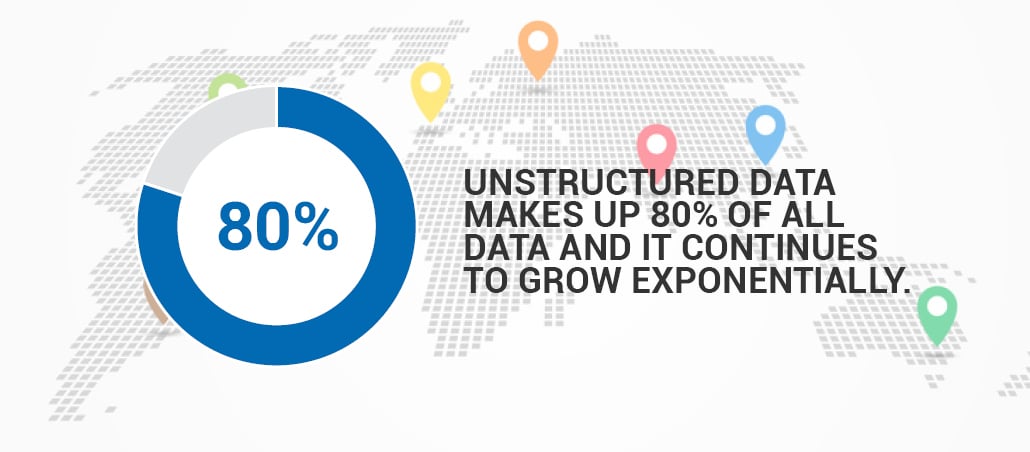
Law enforcement agencies like the FBI receive high volumes of critical information in the form of unstructured data. Gleaning insights…
-

Identity Resolution: a Critical Technology in Anti-Money Laundering
Money laundering is a main risk for financial institutions. An important part of AML due diligence is to screen prospective…
-

Finding the Needle in the Haystack: Entity Extraction and National Security
Intelligence analysts are faced with staggering amounts of unstructured data. Advanced Entity Extraction helps them find the needle in the…
-

Mining Unstructured Data for Competitive Intelligence
In today’s global and fast-paced business world, it’s imperative to monitor one’s competitor landscape closely.
-

How Entity Matching Can Be Critical to Analyze Terrorist Networks
Through fuzzy matching of entity records, Entity Matching uncovers critical connections for the successful social network analysis of terrorist networks.
-

Entity Extraction Makes Open Source Intelligence Analysis Easier
Entity Extraction technology enables organizations to sift through unstructured Open Source Intelligence (OSINT) data swiftly for accurate and timely OSINT…
-

Why Simple Geotagging Software Isn’t Enough to Create a Map from Text
Geotagging software automatically identifies spatial references in text and assigns latitude and longitude values to those. The challenge is the…
-

Three Musts for Link Extraction Software
Link Extraction is an extremely useful technology to mine unstructured data. However, no all Link Extraction software is created equal.
Intelligence Analysis
Filter by
Discover what NetOwl can do for you!
Schedule a demo
Request a no-cost evaluation
Request our whitepaper